We want to alert MyHeritage users about a malicious attempt to steal credentials that we identified several hours ago and is still ongoing.
Perpetrators whose identity is unknown set up a fake website called myheritaqe.com (same as MyHeritage, but with the letter Q instead of the letter G). They started setting up this fake website yesterday, July 20, 2020 according to whois information, which is the date on which this domain was created and registered. They used an anonymity service to hide their identity. They exploited the fact that it’s hard to differentiate between the letters q and g, especially on mobile phones.
We immediately reported this phishing website to GoDaddy.com to have its domain removed and GoDaddy.com are in the process of taking it down. We also reported it to Azure where it is hosted so they could remove it too.
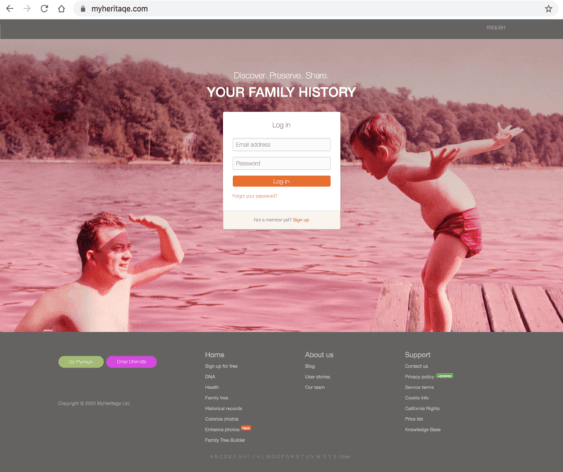
On the fake website, myheritaQe.com, the perpetrators set up a phishing login form to receive login information intended for MyHeritage and harvest the password. The website was made to look like part of the real MyHeritage.com homepage, with all the functionality not working except the fake login. It tries to impersonate the real website.
This is what the fake website looks like:
The perpetrators then started sending a phishing email to email addresses that they apparently compromised from GEDmatch. We don’t know if they emailed (or intend to email) all the users of GEDmatch or only those who uploaded DNA data to GEDmatch that originated from MyHeritage. What we found with all the users they did email, after speaking with these users, is that those users are all using GEDmatch. Because GEDmatch suffered a data breach two days ago, we suspect that this is how the perpetrators got their email addresses and names for this abuse.
One of the users who reported the phishing email had the email copy addressed to another unique name that is not associated with his account on MyHeritage, and that name does not exist on MyHeritage, but it’s the name associated with his account on GEDmatch, which strengthens our suspicion that the account details for phishing were retrieved by the perpetrators from GEDmatch.
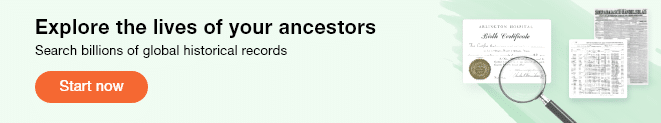
The malicious phishing email sent by the perpetrators has the subject “Ethnicity Estimate v2”, and it looks like this on mobile:

and it looks like this on desktop:

This is a fake email sent by the perpetrators, not by MyHeritage.
If you receive such an email, delete it. Do not click on it.
The email is always sent in English, even to users whose language on MyHeritage is not English.
The email is sent from info@myheritaqe.com and note that it is myheritaqe with a Q and not with a G as it should be. That’s the domain of the perpetrators.
The email has a button called “Review DNA Match”. This makes no sense because the email does not deliver a DNA Match, and the content of the email itself is gibberish, but since the recipients are DNA users (who have been using GEDmatch) they may fall victim to this trap by being intrigued to access something called “Ethnicity Estimate v2” supposedly provided by MyHeritage. This shows that the perpetrators are sophisticated.
This attack has been brought to our attention by a few alert users in social media who started complaining about it several hours ago, realizing that the myheritaQe website is fake.
Because the fake website initially used at least one image file from the real MyHeritage website, we were able to determine that 105 distinct users were lured by phishing to reach the fake website so far. Of these users, we have found that 16 of them have fallen victim to the website and entered their password in it. The number may be higher by now. We attempted to contact each of these users individually to warn them to change their password again and to set up Two-Factor Authentication on MyHeritage.
The website GEDmatch suffered a data breach on July 19, 2020.
See https://thednageek.com/gedmatch-goes-haywire/ and https://cruwys.blogspot.com/2020/07/major-privacy-breach-at-gedmatch.html and https://techcrunch.com/2020/07/19/gedmatch-investigating-dna-profile-law-enforcement/.
We suspect that the data breach on GEDmatch may have included theft of GEDmatch’s user database (at least email addresses and names of customers, perhaps more) and the perpetrators then proceeded to launch a phishing attack against those users from GEDmatch who are using MyHeritage, by sending them a phishing email to try to collect their passwords. It’s possible that the perpetrators did not retrieve the user database in the current breach but had it in their possession from an earlier intrusion into GEDmatch.
This means that the perpetrators may launch a similar phishing attack also against Ancestry and 23andMe, because customers of these websites frequently upload their DNA data to GEDmatch as well, and the names and email addresses of these users may have been compromised on GEDmatch too. We would like to warn Ancestry and 23andme to be vigilant. We don’t know if passwords were stolen from the GEDmatch website or any other information.
Swift action by MyHeritage within minutes of being alerted to this has allowed us to start mitigating the attack. To be on the safe side, we turned off the ability to export DNA data from MyHeritage.
We are monitoring the situation and will alert every user who we become aware of that falls victim to the attack to change their password on MyHeritage. We recommend to MyHeritage users (especially those who are using GEDmatch, but not just them) to set up Two-Factor Authentication on MyHeritage, which means that even if one’s password is compromised, the attacker cannot log in to MyHeritage to access their account. Details on how to do this can be found here: https://faq.myheritage.com/en/article/how-do-i-set-up-two-factor-authentication-for-my-myheritage-account
Beware of the website myheritaQe.com (spelled with a Q). Be suspicious of emails that do not make sense, especially the phishing email with the subject “Ethnicity Estimate v2”. Use a different, unique password on every website – never reuse the same password on multiple websites, and always be vigilant.
We are not aware of any data compromised on MyHeritage. This is a phishing attack that we believe is based on user information stolen in the past 2 days from GEDmatch.
We are continuing to investigate the incident and will update.
UPDATE: On July 21, 2020 at about 9pm PST, Azure took down the phishing website myheritaqe.com and this phishing scam is now over. Stay vigilant.









Robynne Lozier
July 22, 2020
Gosh darn it!!
I got one of those emails and i went off to My heritage to check the ethnicity – but I did not do it through their link, because that just went to the fake home page. Except that I did not know it was fake.
I hate going through the MyH home page, so i chose not to log in through that home page. Instead I went to my heritage the way I normally do.
The fake email claimed an ethinic estimate V2 and when I checked there was no change at all!! Also I managed 4 DNA tests but only ONE person was addressed by this email And yes I am also on Gedmatch!!
Thanks for ths warning.